Computer Security: Brutal AI Threats Crush Defenses 2026
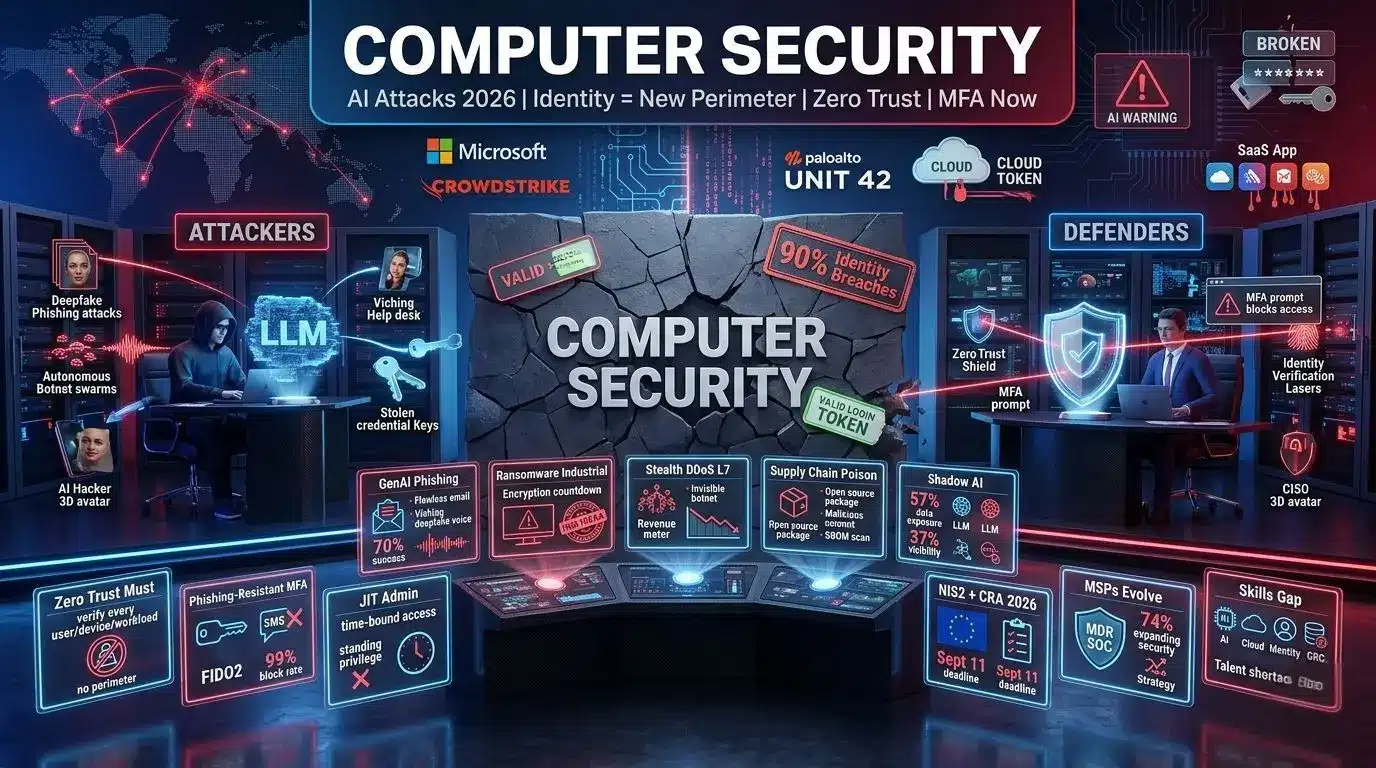
April 2026 is proving that cyber risk is no longer theoretical. It is operational. The computer security landscape shifted because attacks now start with valid access, not exploits. Tricked help desks, stolen credentials, abused SaaS permissions, and approved MFA pushes drive 90% of intrusions. Palo Alto Unit 42 reports identity weaknesses in nearly 90% of investigations. Microsoft confirms extortion drives most attacks. CrowdStrike says intrusions are often malware-free. The computer security problem is trust. Attackers do not break in. They log in.
Healthcare and finance feel it first. HHS OCR announced new HIPAA ransomware settlements this week. The message: “can you prove you understood your risks and acted on them?” The computer security question moved from “were you breached?” to “did you control trust?” Europe’s ESMA warns that AI speeds up attacks. Geopolitical tensions increase risk. The computer security challenge in 2026 is machine-versus-machine warfare, with humans setting intent.
Computer Security: AI Attacks Industrialize in 2026
Generative AI is now a force multiplier for attackers. The computer security threat is industrialized. Ransomware groups and phishing operators weaponize GenAI to create scalable, hyper-realistic, multi-stage attacks. They craft flawless phishing emails, deepfake vishing calls, and debug malware code. LLMs analyze stolen data for maximum extortion leverage. Nation-state actors use GenAI to create fake profiles and evasive malware.
Radware predicts 2026 is the year AI takes its gloves off. Attackers use autonomous AI for prompt injection, synthetic identity abuse, automated reconnaissance, and business logic manipulation. The computer security response must be real AI, not dashboard glitter. Automated triage, autonomous decision-making, real-time mitigation are required. Human response alone is not fast enough. The computer security arms race is AI versus AI.
Computer Security: DDoS Goes Stealth Mode
DDoS is no longer noise. It is sharper, smarter, harder to spot. Attackers use AI to build autonomous botnets that learn in real time. These are calculated, stealthy, and tuned for bypassing mitigation, especially at Layer 7. The computer security threat is not size. It is invisibility. When the application layer slows during a sales cycle, that is a revenue problem, not an IT problem.
Zscaler ThreatLabz says AI-powered attacks hit users, devices, and applications. The traditional perimeter dissolved into a hyper-distributed attack surface. The computer security strategy must be AI-powered and cloud-native. VPNs and firewalls cannot see what is already inside. The computer security gap is identity.
Computer Security: Identity Is the New Perimeter
CSIS warns attackers moved away from malware-led intrusions. They abuse stolen credentials, cloud tokens, and SaaS identities. “Attackers no longer need to break in. They simply log in.” The computer security model shifts from malware detection to identity detection. This bypasses perimeter defenses and compresses attack timelines to minutes.
Kaseya’s 2026 Cybersecurity Outlook says 70% of businesses expect a successful phishing attack in the next 12 months. 40% lost at least a full day to downtime after a computer security incident. Phishing, vishing, and social engineering bypass technical controls by exploiting human trust. In 2026, organizations must treat social engineering as systemic risk.
Read More: Cook Exit: Shocking Reason Tim Cook Leaves Apple 2026
Computer Security: Zero Trust and MFA Are Mandatory
| Control | Why It Matters in 2026 | Implementation Priority |
|---|---|---|
| Phishing-Resistant MFA | Stops 99% of credential attacks. SMS and push can be bypassed. | Admins, IT, finance, execs first |
| Just-In-Time Admin | Eliminates standing privileges attackers love. | All privileged accounts |
| Zero Trust Architecture | Verifies every user, device, workload continuously. | Cloud, SaaS, remote access |
| Identity Threat Detection | Spots token abuse, impossible travel, MFA fatigue. | SIEM + IAM integration |
| Privileged Access Mgmt | Vaults secrets, records sessions, rotates keys. | DevOps, databases, cloud |
The computer security fix is not more tools. It is tighter controls on trust you already give away. Put phishing-resistant MFA on admins first. Eliminate permanent admin rights. Use time-bound access. The computer security ROI is immediate: stolen credentials become useless.
Computer Security: Ransomware at Industrial Scale
CSIS predicts ransomware will operate at full industrial scale in 2026. Intrusion to encryption timelines are shrinking. Attackers automate every phase of the kill chain. Extortion drives most attacks, per Microsoft. HHS ransomware settlements now focus on risk analysis. The computer security question is: did you know your risks and act?
Ransomware is often malware-free. Attackers use legitimate tools and stolen identities. The computer security blind spot is assuming malware will be detected. EDR misses valid users. CrowdStrike confirms intrusions use living-off-the-land techniques. The computer security response must hunt identity abuse, not just files.
Computer Security: Supply Chain Attacks Accelerate
Compromising existing software packages proved highly effective in 2025. That success shapes 2026. Developers who maintain popular open source packages are targeted aggressively. AI makes authentic phishing trivial. The computer security risk: malicious contributions to packages. Shai-hulud style attacks will surge.
Sonatype warns threats will infect a developer’s local environment, compromise trusted packages, and auto-republish malicious versions. AI tooling may adapt malware to the package being republished, complicating static detection. The computer security fix: software bills of materials, signed commits, and automated governance. NIS2 and CRA in the EU mandate it.
Computer Security: Regulations Drive Change
Compliance is no longer a checkbox. It is a design requirement. The EU NIS2 Directive covers critical entities. The Cyber Resilience Act mandates computer security for products with digital elements. Reporting starts September 11, 2026. In the U.S., CIRCIA requires rapid reporting of cyber incidents and ransomware payments.
The computer security trend: boards are accountable. Penalties are significant. Organizations focus on risk management, supply chain computer security, employee training, and transparent incident reporting. Zscaler says meeting frameworks is no longer periodic. Controls must work in practice, with monitoring and ownership across teams.
Computer Security: AI Governance Becomes Critical
94% of CIOs are boosting AI investments, per Logicalis. Yet 50% say the pace is too rapid to manage safely. 57% report employees’ improper use of AI exposes sensitive data. 76% express unease about AI running without checks. Only 37% can see which AI tools their teams use. The computer security blind spot is shadow AI.
Bob Bailkoski, CEO of Logicalis, warns: “AI is a powerful force in cybersecurity, but without the right skills and governance, it can create more vulnerabilities than protection.” The computer securty risk: attackers use AI to bolster cyber operations, craft phishing lures, and automate breaches. CIOs must shield firms from AI-driven threats while navigating risks from protective tools.
Computer Security: MSPs Evolve to Strategic Advisors
Billions are pouring into the MSP market. MSPs evolve from break-fix to specialized, computer security-led, AI-focused service providers. 74% of MSPs plan to expand security services to meet rising client requirements. The computer securty opportunity: clients need help with phishing, ransomware, and downtime.
Kaseya reports 40% of businesses lost a full day to downtime after incidents. MSPs offering MDR, SOC, and identity services win. The computr security shift: from IT support to strategic advisor. Channel Partners Expo shows AI moved from lab to reality. Verizon says customers want real quantifiable business outcomes.
Computer Security: Talent Shortage Hurts Operations
Skills shortages remain structural. Computer security teams face growing complexity while struggling to retain expertise. In 2026, organizations focus on sustainability. They simplify architectures, use managed services, and embed knowledge in processes. Operational continuity becomes as important as innovation.
Nomios says security operations risk becoming black boxes. AI and automation help, but humans set intent and validate outcomes. The computr security workforce needs strategic thinking, AI skills, cloud and identity expertise, zero trust knowledge, and GRC capabilities. National University lists these as 2026 requirements.
Computer Security: How to Respond Without New Budget
Most organizations do not need more tools. They need targeted fixes. The computer security playbook for 2026:
- Identity First: Deploy phishing-resistant MFA for admins, IT, finance, execs. Remove standing admin. Use JIT access.
- Zero Trust: Verify every session. Segment networks. Assume breach.
- Supply Chain: Require SBOMs. Scan dependencies. Sign artifacts.
- AI Governance: Inventory AI tools. Block unapproved LLMs. Monitor data flows.
- Social Engineering Defense: Run realistic simulations. Train on vishing. Use behavioral analytics.
- Incident Readiness: Test backups. Run tabletop exercises. Document risk decisions.
The computer security truth of 2026: compromise is no longer hypothetical. It is happening. April was one of the most painful months for breaches. Attackers do not need zero-days. They need your password. The computr security win is making that password useless.
FAQ Section
1. What are the biggest threats in 2026?
AI-powered phishing, identity-based intrusions, ransomware, supply chain attacks, and stealth DDoS. Attackers use valid credentials instead of malware.
2. Is AI helping or hurting defense?
Both. AI improves threat detection and automation. But attackers also use it to create realistic phishing, automate recon, and bypass defenses.
3. What is Zero Trust Architecture?
A model that replaces perimeter security with continuous verification. Every user, device, and workload is checked before access, even inside the network.
4. Why is MFA not enough?
SMS and push MFA can be bypassed via fatigue attacks or SIM swapping. Phishing-resistant MFA like FIDO2 or passkeys is needed for admins.
5. How does ransomware work without malware?
Attackers log in with stolen credentials, use legitimate admin tools, and encrypt data. EDR does not detect valid users doing admin tasks.
6. What regulations matter in 2026?
EU NIS2, Cyber Resilience Act, and U.S. CIRCIA. They require risk management, incident reporting, and secure product design.
7. What skills do security jobs need?
Strategic thinking, AI and automation, cloud and identity security, zero trust, and GRC. Technical skills alone are not enough.
8. Should small businesses worry?
Yes. 70% expect phishing to succeed. 40% lost a day to downtime. MSPs are key partners for security services.

Meet Md. Rubel Rana
As a core contributor to Worlddincidents.com, Rubel Rana brings a unique perspective to the world of journalism. Whether it’s deep-diving into historical trivia or covering the latest global headlines, Rubel Rana is committed to delivering high-quality, high-impact articles. Their writing blends meticulous research with a compelling voice, helping readers stay informed and curious about the world around them.